As vehicles continue to evolve and become deeply interconnected, it's essential to establish consumer trust in automotive cybersecurity.
With a staggering 40.7 million vehicles traversing UK roads and technology advancements accelerating, your organization's role in this landscape is paramount.
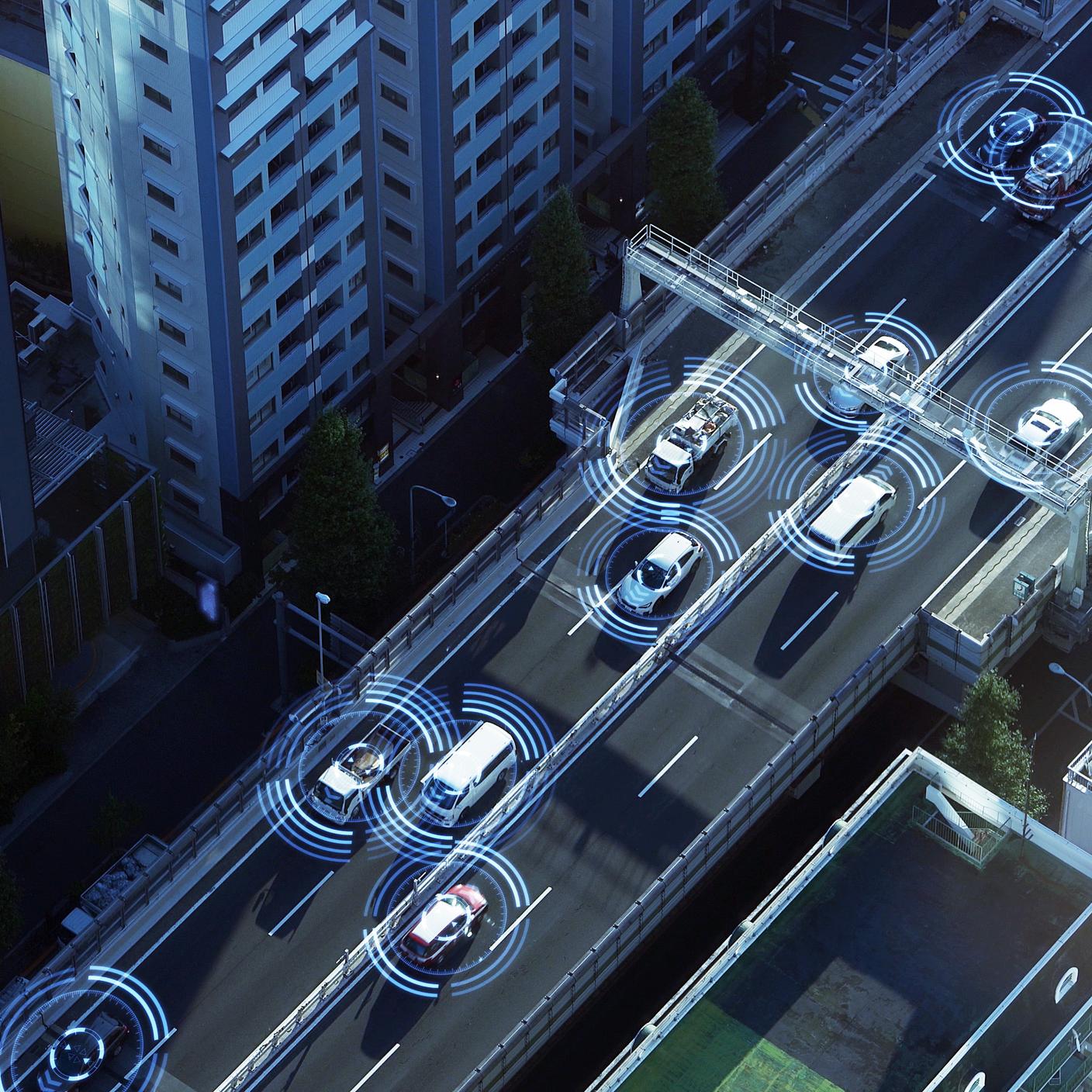
From sophisticated onboard computers to digital parking aides, cars are embracing smarter technology. However, this smart evolution demands robust cybersecurity measures to ensure user safety and thwart potential cyber threats.
Whether it's safeguarding against vehicle theft or preventing safety system breaches that could lead to accidents, the significance of cybersecurity in the automotive realm cannot be overstated.
Your organization can play a pivotal role in shaping a secure and trustworthy automotive future.
Which automotive systems require cybersecurity?
Modern vehicles are highly digitized, and have even been referred to as “computers on wheels”.
Digital systems can include:
• Parking sensors and cameras
• GPS systems
• Bluetooth-connected radios
• Keyless entry systems
• Automatic lane-keeping systems (ALKS)
• Advanced driver assistance systems (ADAS).
Entire vehicles can be digitized too, such as fully connected and autonomous vehicles (CAVs).
There are networks within vehicles called controller area networks (CAN) which help various electronic systems communicate with each other.
In recent years, CAN interfaces have dramatically advanced to include Bluetooth, Wi-Fi, digital audio broadcast (DAB) and complex software models to help everything run smoothly. And with that much connectivity comes challenges as well as opportunities.
Vehicles also produce data of their own, through electronic control units (ECUs), CANs and even the radio system.
Most of that data is held in cloud storage and can be sent to insurers to help design products and premiums. But some of the data is personal identifiable information (PII), such as drivers’ names, addresses and identities, and could be at risk of being stolen through a digital hack.
What is hackable?
Car manufacturers Hyundai and Kia have both recently responded to car theft hacks circulating on social media by issuing software upgrades. And 16 other car manufacturers, including BMW and Rolls Royce, had vulnerabilities in their vehicles’ internal applications and systems that showed it was possible to expose the owner’s PII.
The hacks targeted the vehicles' telematics systems. Keyless entry systems can also be hacked, as some cars can be unlocked using a driver’s smartphone, as well as interconnected apps that can be left exposed to hackers, such as connected music accounts on Spotify.
These weak points in cars can leave drivers at risk in more ways than one. Cars’ vehicle identification numbers (VIN) have been used by researchers in a test to see what could be hacked.
The researchers managed to:
• Start and stop engines
• Remotely lock and unlock vehicles
• Retrieve precise locations of certain models
• Change car ownership
A car’s VIN – the data the researchers used – is usually visible on a windscreen. This number was all the researchers needed to manipulate the digital systems and access customer accounts.
How can your supply chain be prepared?
So, what can your supply chain do to build consumer trust?
By addressing cybersecurity within the sector, compromises can be avoided, helping your consumers make informed decisions about the vehicles they buy or lease.
According to McKinsey, employees in the automotive sector must be ready to learn new skills and ways of working throughout the development cycle to ensure a cybersecurity mindset in the future.
There are also new standards and guidelines being created to secure both hardware and software in vehicles.
The UNECE Working Group 29 has introduced Cyber Security and Cyber Security Management System (UN Regulation No.155). This regulation mandates compliance with the cybersecurity standard for road vehicles (ISO/SAE 21434), as a prerequisite for market supply.
ISO/SAE 21434 strives to establish a universal language within the automotive industry, ensuring that cybersecurity is unified under shared terminology, fostering transparency and enhancing comprehension. By harmonizing UN requirements with standardization, your supply chain can bolster its security, creating a safer environment for consumers and promoting increased trust.