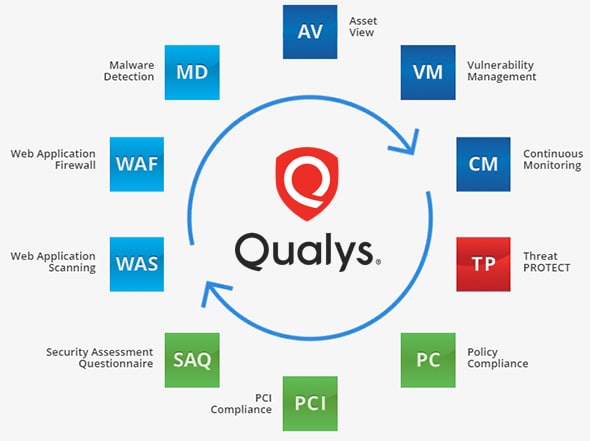
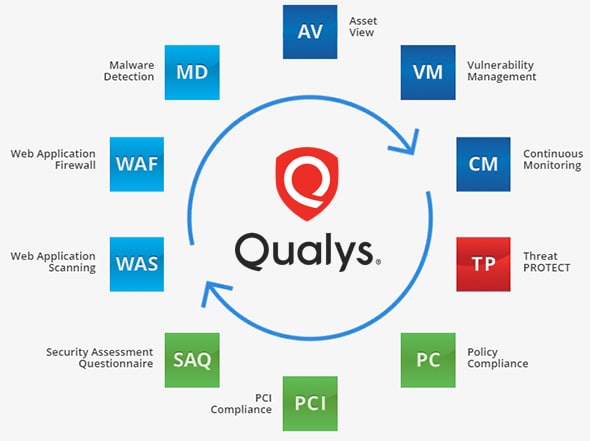
Built on top of Qualys’ Infrastructure and core services, the Qualys Cloud Suite incorporates the following applications, delivered via the cloud.
Asset discovery
Find and catalogue all your IT assets wherever they reside.
Qualys’ Asset View (AV) module consolidates all asset details in a centralized browser-based, customizable dashboard. It gives organizations a real-time view of their increasingly distributed and varied IT environments, so they know where assets are located, who manages them and what security risks they carry.
This inventory is updated in real time without the need for proactive polling.
Network security
Qualys provides full visibility of IT assets across all networks — on premises, in the cloud and on mobile endpoints — to highlight how they might be vulnerable and facilitate with protection.
- Qualys Vulnerability Management (VM) continuously identifies exposures so organizations can defend themselves against attacks wherever and whenever they appear
- Qualys Continuous Monitoring (CM) alerts in real time about network irregularities, such as new hosts/operating systems, expiring certificates, unexpected open ports and unauthorized software
Threat protection
Prioritize vulnerability remediation work with Qualys Threat Protect.
Qualys addresses the overload of vulnerability and threat disclosure by automating the large-scale and continuous data analysis that the process demands.
Qualys continuously correlates real-time threat information against vulnerabilities and IT your asset inventory, giving a clear and comprehensive view of your organization’s threat landscape.
Compliance monitoring
Qualys' compliance monitoring solutions automate the complex task of assessing procedural and technical controls for vendor risk management, internal IT compliance, and general best practices for securing IT systems.
- The Policy Compliance (PC) module performs security configuration assessments on IT systems throughout the network
- The PCI module checks specifically for compliance with the Payment Card Industry Data Security Standard (PCI DSS), including the requirement for organizations to maintain secure web applications
- The Security Assessment Questionnaire (SAQ) streamlines an organization’s vendor risk management process, including the design, distribution, tracking, aggregation and management of multiple internal and external risk assessment surveys from a web-based central console
Web app scanning
Boost web app security with Qualys' cloud-based, integrated solutions.Qualys automates web app security, shields web servers from hackers, gets rid of malware from websites and makes the software development lifecycle more secure.
- Qualys Web Application Scanning (WAS) crawls and tests custom web applications to identify vulnerabilities, while its extensive APIs let users integrate scan data with other security systems
- Qualys Web Application Firewall (WAF) blocks attacks on web server vulnerabilities, and faciltitates control of where and when applications are accessed
- Qualys Malware Detection (MD) proactively scans an organization’s customer-facing websites for infections, triggers automated alerts and generates detailed reports
 solutions that leverage shared and extensible core services and a highly scalable multi-tenant cloud infrastructure:
solutions that leverage shared and extensible core services and a highly scalable multi-tenant cloud infrastructure: