Benefit from relevant courses that are continually updated with the latest global trends and regulatory changes.
- Search BSI
- Verify a Certificate
Suggested region and language based on your location
Your current region and language

Gain the knowledge and skills to add more value to your organization, whilst developing your career.
Benefit from relevant courses that are continually updated with the latest global trends and regulatory changes.
Find the right courses or qualifications for you and your team. Start building the skills and experience to embed best practice today.
With awareness and requirements courses, you'll be guided on the key terms, definitions, and foundations of a standard.
Browse courses
These courses are ideal for those responsible for embedding a management system in their organization.
Browse courses
Learn to plan, conduct, report and follow up an audit, whether internal or part of a wider-scale management system audit.
Browse courses
You and your team will all learn in different ways, so we’ve devised a range of flexible delivery formats to suit all needs.

Find the right courses or qualifications for you and your team. Start building the skills and experience to implement best practice today.
This icon indicates where a course forms part of a qualification pathway. Toggle to Qualifications to show the Qualification choices.
Get answers to frequently asked questions and find out about our most popular ISO and business improvement training courses.
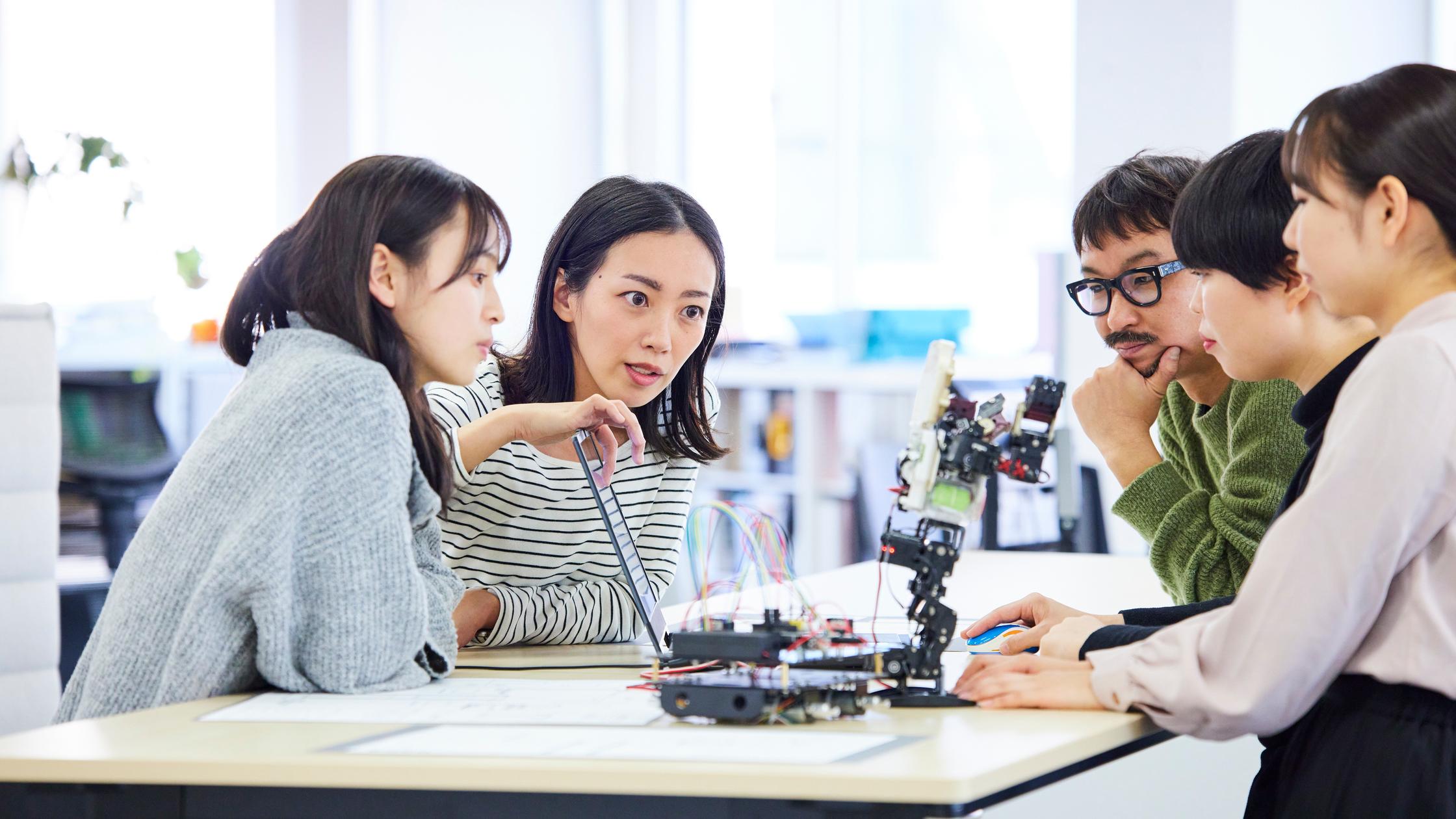
Build your career by upskilling on key ISO standards. Learn self-paced, or join like-minded learners face-to-face or via an online classroom.
Download Brochure

Structured training, delivered to your team in-house or in a live, virtual classroom. Save on each individual delegate and eliminate travel expenses.
Get in touch

Your organization, your training programme. Our partnership approach ensures learning is designed to facilitate your strategic objectives.
Get in touch
Speak to our training advisors on +852 3149 3300.
Access impactful learning on key topics and challenges facing organizations today.
See all coursesProtecting information and creating digital trust for customers and your supply chain is increasingly important.
Find out more
Gain an awareness of the systems, tools and techniques to implement and audit against a variety of standards.
Find out more
Build the confidence and competencies to minimize occupational and health risks to all stakeholders.
Find out more